Now - 20:28:32
Methods and means of information protection
The Methods and means of computer information protection is a set of various measures, hardware and software, ethical and legal standards, which are intended to counteract threats of attacks and to minimize possible damage to system owners and users of information.
Consider the following varieties of traditional measures to counter the leakage of information from the computer.
Technical methods and means of information protection
This includes:
- Protection against unauthorized access to a computer system;
- Backup all your important computer subsystems;
- Networking with the possibility to reallocate resources if there is a malfunction of individual network links;
- Installation of equipment for detecting and extinguishing fires;
- Installation of equipment for detection of water;
- The adoption of measures to protect against theft, sabotage, sabotage, explosions;
- Installing the backup power system;
- Equipping the premises with locks;
- Alarm.
Organizational methods and means of information protection
This includes:
- Protection servers
- Carefully organized recruitment;
- An exception of such cases, when all critical work is performed by one person;
- Develop a plan to recover the server in a situation when it fails;
- Universal protection from any user (even senior management).
Methods unauthorized access to information
The above is not Enough to know methods and means of information protection, it is necessary to understand how they can be made to information unauthorised access.
Note that unauthorized access of important information can occur during the repair or maintenance of computers due to the fact that the residual information in the media can be read, despite the fact that the user promptly removed it the normal method. Another way – when information is read from the media, if it is transported without protection.
Recommended
How to get out of "Skype" on the "Android" and not only
How to get out of "Skype" "Android"? This question bothers many users. The thing is that the messenger is not so difficult. But there are features that are only for mobile versions. To log out of Skype in this case more difficult than it seems. But i...
Kingo ROOT: how to use the program to gain administrative rights on Android
The Gadgets on the platform Android regained the lion's share of the market. Developers are continually perfecting the OS, trying to fit the needs of the users, but from year to year admit palpable mistake: forbid the owner to "stuffing" of his gadge...
How to get from Stormwind to Tanaris: practical tips
World of Warcraft is an iconic MMORPG, uniting millions of players around the world. There are many locations and puzzles, secret trails and larger, but rather dangerous paths. Sooner or later, every player chose the side of the Alliance, we have to ...
Modern computers based on integrated circuits, in which implemented high-frequency changes in the levels of currents and voltages. This leads to the fact that power circuits, nearby equipment, ether, etc. there are electromagnetic fields and interference which are some “spyware” technical means can easily be transformed into information that is processed. Thus, the smaller the distance from the receiver of the malefactor to the hardware, the more likely that to remove and decrypt information succeed. Introduction to information bearing unauthorized, and possibly also due to the direct connection by an attacker “spyware” means to network equipment and communication channels.
Methods and ways of information protection: authentication and identification
Identification is the assignment of subject or object a unique image or name. And authentication is to check whether the subject/object who is trying to give itself. The ultimate goal of both measures – the admission of the subject/object to the information that is in limited use or denial of such permit. The authenticity of the object may be a program, hardware device or person. The objects/subjects of authentication and identification can be: hardware (workstations, monitors, subscriber stations), people (operators, users), the information on the monitor, magnetic media, etc.
Methods and means of information protection: the use of passwords
Password is a set of characters (letters, numbers, etc.), which is designed to determine the object/subject. When there is a question about what password to choose and install, the question always arises about the size, the method of application of resistance to the selection by an attacker. It is logical that the longer the password, the higher the level of security it will provide to the system, as it will take much more effort for him to guess/pick up combination.
But even if the password is a strong password, it must be periodically replaced with a new one, to reduce the risk of interception with the direct theft of the carrier or the withdrawal from media copy, either by violent force the user to say “magic” word.
Article in other languages:
AR: https://tostpost.com/ar/cars/7586-what-is-the-exam-in-the-traffic-police.html
BE: https://tostpost.com/be/a-tamab-l/13550-shto-zh-uya-lyae-saboy-ekzamen-u-d-bdr.html
DE: https://tostpost.com/de/autos/13553-was-ist-eine-pr-fung-in-der-verkehrspolizei.html
ES: https://tostpost.com/es/coches/13560-que-es-un-examen-en-el-gbdd.html
HI: https://tostpost.com/hi/cars/7592-what-is-the-exam-in-the-traffic-police.html
JA: https://tostpost.com/ja/cars/7588-what-is-the-exam-in-the-traffic-police.html
KK: https://tostpost.com/kk/avtomobil-der/13553-b-l-b-ld-red-emtihan-gibdd.html
PL: https://tostpost.com/pl/samochody/13540-co-to-jest-egzamin-do-policji.html
PT: https://tostpost.com/pt/carros/13534-o-que-um-exame-de-pol-cia-de-tr-nsito.html
TR: https://tostpost.com/tr/arabalar/13556-nedir-bu-s-nav-traf-k-polisi.html
UK: https://tostpost.com/uk/avtomob-l/13550-scho-zh-yavlya-soboyu-spit-v-gibdd.html
ZH: https://tostpost.com/zh/cars/8252-what-is-the-exam-in-the-traffic-police.html

Alin Trodden - author of the article, editor
"Hi, I'm Alin Trodden. I write texts, read books, and look for impressions. And I'm not bad at telling you about it. I am always happy to participate in interesting projects."
Related News
How to enable Bluetooth on a laptop "ASUS"? Program Bluetooth
well, today we have to understand how to enable Bluetooth on a laptop "ASUS". There are several options, and they are quite easy to learn. To resolve the issue can even novice user. However, have to understand some of the nuances....
"I farmleigh" what does that mean? How quickly and correctly to farm?
Making the first steps into the virtual reality of the game, a beginner is always confronted with difficulties. Some are confused about the buttons, others don't understand the ability of the character, others can not adequately c...
USB microphones review, specifications, tuning
Choose a good quality USB microphone is not as easy as it seems at first glance. There are many different models that entice the buyer, not only nice price and impressive performance, in fact, find themselves just a marketing ploy...
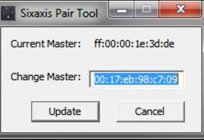
How to connect Dualshock 3 to the PC?
Who would have thought that the standard game controller for the Playstation 3 from Sony will be interested in the owners of personal computers, which at hand is a convenient input device: mouse and keyboard. From this article the...
How to find out your efficiency in World of Tanks?
Gamers are sometimes confused World of Tanks with the shooter, they believe that all that is matters is the number of killed enemy tanks. However, this is the biggest misconception, because in WoT the most important thing is the a...
"Stalker: Bad company": passing modifications
the Game "Stalker" was one of the most successful in the post-Soviet space in recent years, in most cases they did not receive much fame. But the "Stalker" has become incredibly famous worldwide, but this is not important. The mos...




















Comments (0)
This article has no comment, be the first!