Now - 08:01:11
What is deamon? Deanonimizatsiya of users of social networks. Personal data
If you think this deamon, and it is worth to learn only for the overall development, it is deeply mistaken. Every Internet user should at least be informed about the basic rules for its safe use.
Teens use the benefits of the virtual world permanently, because more versed in these issues. But even young, “advanced” generation can make trouble, if not will delve into the question of digital security.
The world wide web so much “healed” with our usual existence, that the consequences of such interactions can be more serious than everyone is used to count.
What does the word “deanonimizatsiya”
What is deanon (deanonimizatsiya)? Is this word in two parts, anonymous, and the prefix de-, which indicates a denial. Means that clearly, the process of violation of the status “anonymous” by the user or other people (using methods deanonimizatsii).
In Simple words - when personal data are made public. Personal include anything from baby photos to work.
Even cautious Internet users are a lot “marks” of their stay. For those who have asked the question of declassification, and sometimes do not have too much to go into the search. Often the information is in different open sources. And just need to know where to look.

Basic terms that relate to deanonimizatsii
To understand further explanation, what is deinon, and in what ways find people's personal data should know the key terms:
- User-any person, which uses the Internet and has any profiles, registration.
- Anonymization-the process of hiding their personal data.
- Anonymity – when a character on the Internet is not related to any real person.
- Profile – the personal user page in social networks, on other sites, which contain personal data.
- Nickname-a nickname that the user has installed on the Internet .
Recommended
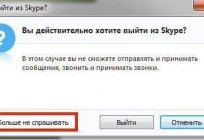
How to get out of "Skype" on the "Android" and not only
How to get out of "Skype" "Android"? This question bothers many users. The thing is that the messenger is not so difficult. But there are features that are only for mobile versions. To log out of Skype in this case more difficult than it seems. But i...
Kingo ROOT: how to use the program to gain administrative rights on Android
The Gadgets on the platform Android regained the lion's share of the market. Developers are continually perfecting the OS, trying to fit the needs of the users, but from year to year admit palpable mistake: forbid the owner to "stuffing" of his gadge...
How to get from Stormwind to Tanaris: practical tips
World of Warcraft is an iconic MMORPG, uniting millions of players around the world. There are many locations and puzzles, secret trails and larger, but rather dangerous paths. Sooner or later, every player chose the side of the Alliance, we have to ...
What data you open when registering
Deanonimizatsiya of users in 95% of cases is based on the data that they inadvertently spread in the General access. When you register anywhere your profile and fill the details then submit personal information to not only the administration, but of all who will be able to retrieve it.
Normally, a profile on the site or the forum has at least a few points. Consider what data you usually tell yourself:
- Date of birth. This option is available in most profiles. Even if you said “no date of birth in the application form”, the information still can “float”. For example, because the corresponding nickname (Pavel1991). Or surfaced thanks to the warning “today is the birthday N”.
- Country, city. Usually the exact address is not listed anywhere (except online stores). But for small towns it is enough one name. Then you will have can be found in open databases, or even just the friends list.
- Mail. Many do not consider the mailbox address in the personal information, but in vain. The very “name” box may already contain references to other personal information (like birth year, in the example above). Through Inbox you can find other resources in which you are registered.

What methods are used to deanonimizatsii
What is deanon you already knew. But what methods are used to bring people to "clean water”?
- Photos. The image search and the use of certain services will allow you to find information about a person's photos. So the more you use the same frame on different sites, the easier it will be to link them all together.
- Nicky. The same applies to nicknames. Users don't like to remember different logins and passwords so often use the de data. When deanonimizatsii they can easily be combined.
- Speech. When you "dig deeper" in the course can go even with the analysis of speech features. Our texts, use of specific words and terms, punctuation, give head the level of human development. The style of writing quite difficult to fake.
- Working. Workers narrow profile can easily be calculated through a separate professional websites and resources, and the use of expert terminology or materials.
- Friends List. Your list of friends on the same resource without problems “restore” your personality on the other. Even if there won't be any information about you or it will be replaced by false.

Deanonimizatsiya and social networks
What is deinon in "VC"? You already know what that means creating a link between the fake social network user and a real person. Perhaps no other complete source of information about the user, his profile "Vkontakte". Here is a list of friends, and the place of study or work, and personal interests.
This social network is also associated with a number of others. So, finding a person inCS, it is possible to obtain almost complete his portrait.
The same can be said about the social network Facebook. Matter how carefully the developers had not belonged to the keeping of personal data, some information they missed. For example, it is necessary to go to the password recovery page and enter your e-mail “victim”, "Facebook" helpfully show you the name and avatar of the person.

What is dangerous deanonimizatsiya
The threat deanonimizatsiya for stars, politicians, major employers, it's understandable. Accidentally leaked private information, which can be linked to a known person, – often, a cross throughout his career. Or, at least, a serious stain on it. But why know ordinary people who do not hide special secrets?
First of all, each of us leaves in the network traces of their stay. And after a while some of them are unpleasant facts or evidence of error. For example, when talking about the use of thematic forum, which you don't want to admit it. Or public evidence of your Internet love, which ended unfortunately. Everyone makes mistakes, and there is nothing to worry. But it is frustrating when these ghosts of the past emerge. Especially when they finds someone they are not.
Also private information can “extract” and use the crooks. For example, the forum of young mothers you discussed with friends, what to take on vacation, you are going the whole family in a week. What I see in this correspondence scams? That your apartment will be empty. The only thing you need – to calculate the address of your residence (and today's technology does allow you to do this easily). In this case, the price deanonimizatsii can be very high!
About deanonimizatsiyu we must not forget those who are looking for work. The personal data of the users "Vkontakte" will not always look good in the eyes of the HR Department. For example, the posts that you had problems with the boss on the last job. Or the abundance of groups with erotic content. Against you can “play” even the friends list! the
Nowadays, everyone has the right to decide what tactics to choose carefully hide all your data or safely use the Internet and be one of a million people. In any case, everyone needs to know what deanon. The young generation must be careful to treat the dissemination of personal data, and the high – to teach their children and control them.
Article in other languages:
AR: https://tostpost.com/ar/computers/14234-deamon-deanonimizatsiya.html
HI: https://tostpost.com/hi/computers/14256-deamon-deanonimizatsiya.html
JA: https://tostpost.com/ja/computers/14258-deamon-deanonimizatsiya.html
ZH: https://tostpost.com/zh/computers/14908-deanonimizatsiya.html

Alin Trodden - author of the article, editor
"Hi, I'm Alin Trodden. I write texts, read books, and look for impressions. And I'm not bad at telling you about it. I am always happy to participate in interesting projects."
Related News
How to recover files from USB drive by yourself?
the USB drive is considered a very reliable media, but even he cannot guarantee its absolute safety. Failures that affect this type of drive can destroy any recorded to a USB drive file. How can to restore files from USB drive? Th...
Today we will tell you about the famous Dota 2 player, who calls himself: Admiral Bulldog. Actually his name is Henrik Enberg, and he is a very mysterious person. The project “Bunker” believed to be an integral part of...
Cable (marvel): overview, characteristics of character and interesting facts
the universe ‘marvel’ is full of a variety of superheroes, among which there are both good and bad. The series has a few favorites such as Spider-Man, Deadpool, Wolverine and so on, but there are also less known but no...
The Atmega8. Programming Atmega8 for beginners
the Atmega8 are the most popular representatives of his family. In many ways they owe, on the one hand, ease of operation and straightforward structure, with another - quite wide functionality. This article looks at the programmin...
We produce network cable with your hands
I Think everybody knows what a network cable. With it, you will be able to combine the two computers directly or to connect to the network. In this article I want to tell you how to make a network cable with your hands. It is very...
Where to enter cheats in Clash of Clans and is it possible?
"clash of clans" is one of the most popular multiplayer computer games. It is distributed on mobile platforms or through social networks, so you don't have to download a large client, and wait for loading for a very long time. Man...





















Comments (0)
This article has no comment, be the first!